When anyone talks about auditing, most technical people immediately believe in vulnerability scanning or auditing. There are two major tools/frameworks when it comes to Linux vulnerability scanning, OpenVAS vs. OpenSCAP.
While they have things in common, there are also quite a few differences. In this blog post, we will differentiate between OpenVAS and OpenSCAP.
In broad terms, OpenSCAP is a tool to assist administrators and auditors with assessment, measurement, and enforcement of security baselines whereas OpenVAS is a defined framework of many tools contributing to vulnerability scanning as a solution.
Both the tools are commonly used for penetration testing, security assessment, or vulnerability scanning. More so, pen-testers and security professionals are target users for both.
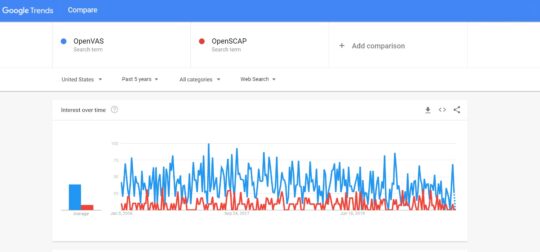
From the above Google Trends screenshot, it can be evaluated that OpenVAS is leaps ahead of OpenSCAP in terms of customer preferences.
SCAP aka Security Content Automation Protocol is a standard governed by the NIST.
It was created to provide a uniform approach to maintaining safety across enterprise systems, like naturally verifying the presence of security patches, checking the system’s configuration settings, and examining the system’s security for any signs of weakness.
The word ‘Open’ in OpenSCAP stands for being open-source.
Key Features
- Uses command-line interface.
- More than 25 contributors.
- The source code of this software is available.
- Uses CWE naming conventions.
According to the OpenVAS website, it is a full-featured vulnerability scanner.
The Open Vulnerability Assessment System is a framework of multiple services and tools offering a substantial and extensive vulnerability scanning & vulnerability management fix.
Its abilities include unauthenticated and authenticated testing, various other high-level as well as low-level Internet protocols, and a strong internal programming language to implement any sort of vulnerability test.
The scanner performs vulnerability tests with detailed report consisting of daily updates. This OpenVAS scanner is developed and supported by the Greenbone Networks from 2009.
Originally, Greenbone's business plan had 3 capstones:
- Go beyond plain vulnerability scanning towards a general and extensive vulnerability management solution.
- Create a multi-utility appliance product for enterprise customers.
- Continue the Open Source concept of making transparent security technology.
Also Discover: 7 Alternatives to OpenVAS
OpenSCAP is listed under the Linux hardening tool and Linux security audit tool. Whereas, OpenVAS is categorized as a Linux vulnerability scanning tool, vulnerability management tool, and vulnerability scanner.
In the field of Linux systems, OpenVAS is essentially an open-source vulnerability scanner and OpenSCAP, an open-source auditing scanner. Both tools have the purpose to find any security-related weakness in the system.
Where the former does a wide range of tests from the network, the latter is a standard in itself. Both tools will detect different findings, depending on the services offered.
OpenSCAP is supported by a bigger organization such as Red Hat, while in comparison OpenVAS itself is a well-known tool.
Both the tools work on the Linux operating system and are coded in the C programming language.
OpenSCAP and OpenVAS both are open-source, supported by a community with seasoned contributors and broadly listed in Exploit Prevention Suits & Softwares.
OpenVAS:
OpenVAS released GVM-10 which comprises many performance optimization features to deal with a growing number of vulnerability tests, scanning target networks of growing size and heterogeneity.
In 2020, OpenVAS released with GVM-11 that introduced substantial command line changes i.e the former service "openvassd" has been converted into a command-line tool called the "openvas".
OpenSCAP:
- Added support for FreeBSD.
- New features.
- Using HTTP header content-encoding: gzip (if available)
- A lot of memory leaks have been plugged.
- Fixed DOM representation of the profile platform.
- Test suite for better maneuverability, more specific in results, and the inclusion of memory-related tests.
- The local and remote filing system detection method was improved.
Conclusion
OpenVAS perform a group of tests against the HTTP or HTTPS port and reveal its outcomes.
While that is a good thing, it might be missing that your system time is not properly synced. These kinds of things can be detected by OpenSCAP.
So in the end it is not wise to compare vulnerability scanners and auditing tools with each other, as their aim is different. If you would compare something, then compare OpenVAS with Nessus. For OpenSCAP you could compare it with Lynis.
Often, organizations opt for both and leverage the advantages of both to extract the highest level of productivity possible.
You may also like to read: List of 5 Open Source Vulnerability Scanner Tools