There are different types of Intrusion Detection Systems (IDS) for the protection of networks. But why do we need an IDS? There are various personal and professional data on the internet these days. Hence, IDS makes sure this data is safe from malicious activities and from policy breaching. It alarms the user about suspicious activity.
Intrusion attacks are becoming more common on a global scale. In addition, hackers are trying new techniques to hack into a system. IDS is a tool that will identify these attacks and will take immediate steps to restore the system to normal. IDS will also detect network traffic and send an alarm if an intrusion is found.
Different Types of Intrusion Detection Systems (IDS)
What is an Intrusion Detection System (IDS)?
An Intrusion Detection System is a software or a system that monitors network traffic and detects an intrusion or unwanted activities in the network. IDS scans the networks to find out if someone is trying to penetrate the network illegally. In other words, it keeps an eye on the network's traffic to identify intrusion in the network.
Intrusion Detection System if properly configured will help you to:
- Monitor inbound and outbound network traffic.
- Analyze the patterns in the network continuously.
- Send an alarm immediately after detecting unwanted intrusion and activities in the network.
Organizations must properly install IDS into their system. The IDS must analyze the normal traffic on the network. However, if IDS does not analyze the normal traffic properly then it might send a false alarm in case of intrusion.
Different Types of Intrusion Detection Systems
Different types of Intrusion Detection systems are classified on the basis of different techniques and methods.
Network Intrusion Detection System (NIDS)
Network Intrusion Detection System sets up across the network at a specific planned point. NIDS monitors the traffic on the network from all devices. Similarly, it examines the traffic passing on the entire subnet and verifies it with the packet metadata and content. If NIDS detects any intrusion in the network, a warning alert is sent to the admin of that network. The best advantage of NIDS is that if it is installed in the same location where the firewall is located, then it will detect if someone is trying to attack the firewall. In other words, with the help of NIDS, the firewall will also be protected from any policy breaching.
Host Intrusion Detection System (HIDS)
Organizations install a Host Intrusion Detection System (HIDS) on independent networked devices. However, HIDS examines the incoming and outgoing traffic of the device only. It detects suspicious activities on the device and alerts the administrator. HIDS also checks whether system files are misplaced or not, for that it takes the screen capture of the current file system and verifies it with the screen capture of the previous file system. This file system stores the analytical information of network traffic. For instance, if the files are misplaced or changed it sends an alert to the administrator.
Protocol-based IDS (PIDS)
Organizations set up a Protocol-based Intrusion Detection System at the front end of the server. It interprets the protocols between the server and the user. PIDS monitors the HTTPS server regularly to secure the web. Similarly, it allows the HTTP server which is related to the protocol.
Application Protocol-based IDS (APIDS)
As we have seen that PIDS is set up at the front end of the server. Similarly, APIDS is set up within a group of servers. It interprets communication with the applications within the server to detect the intrusion.
Hybrid Intrusion Detection System
As the name says Hybrid Intrusion Detection system is a mixture of two different IDS. Hybrid System develops a network system by combining host agents with network information. In conclusion, Hybrid System is more responsive and effective as compared to other IDS.
Types of Intrusion Detection Systems Methods
There are 2 main Intrusion Detection methods to identify malicious attacks or intrusion. However, both these methods serve a different purpose and are not similar.
Signature-based Intrusion Detection Method
The IDS developed the Signature-based intrusion detection method to examine the network traffic and to detect attack patterns. For instance, it verifies the network traffic with the log data to identify the intrusion. If this method detects any intrusion then the IDS solution creates a signature of it and adds it to the list. The patterns which are detected are known as sequences and these sequences are a specific number of bytes or a set of 0’s and 1’s in the network. However, it is easy to detect the attacks whose patterns are existed in the system in the form of signatures. But to detect new attacks whose signature is not yet created is difficult.
Anomaly-based Intrusion Detection Method
As we have seen that it is difficult to detect unknown or new malware attacks with the help of the Signature-Based Detection method. Therefore, organizations use the anomaly-based intrusion detection method to identify those new and unknown suspicious attacks and policy breaching which the Signature-based detection method cannot identify easily.
However, new intrusion techniques and malware are increasing rapidly. This method uses Machine learning to create an activity model. If this method detects any receiving patterns which are not found in the model, then the method declares these patterns as malicious patterns. In conclusion, the anomaly-based detection system is better in comparison to the Signature-based method.
Hybrid Detection Method
A Hybrid method uses both Signature and Anomaly-based intrusion detection methods together. However, the main reason behind the development of a hybrid detection system is to identify more potential attacks with fewer errors.
SolarWinds Security Event Manager
SolarWinds designed this tool with the implementation of HIDS and NIDS systems. It collects real-time log data from the network. Similarly, SEM is popular to build customizable intrusion detection methods which can automatically disable accounts and disconnect the devices attached to the network it detects any intrusion.
Free Trial: 30 Days.
McAfee
McAfee designed its IDS to identify real-time malicious activities. It uses both signature and anomaly methods to identify the threats with emulation techniques. Therefore, McAfee is a scalable application.
Free Trial: 30 Days.
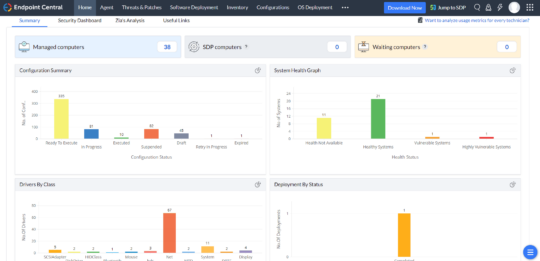
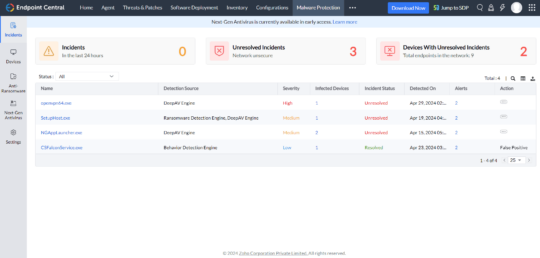
Endpoint Central
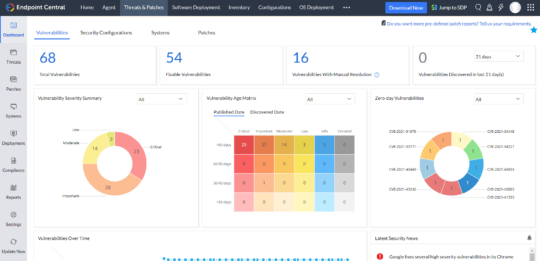
ManageEngine Endpoint Central is a cutting-edge Unified Endpoint Management and Security (UEMS) solution designed to streamline and safeguard the modern-day digital workspace distributed across various device types and operating systems. The solution employs a single lightweight agent, providing comprehensive device lifecycle management alongside robust security functionalities like real-time threat detection and containment mechanisms. By enabling businesses to secure their endpoints while limiting IT blind spots effectively, Endpoint Central enhances operational efficiency, boosts user experience, and integrates audit compliance measures.
Using AI-assisted real-time behavioral detection and deep learning, Endpoint Central's next-gen antivirus (NGAV) and anti-ransomware capabilities are crucial in defending against evolving cyber threats, proactively identifying and neutralizing malicious activity before it can compromise systems. Combined with automated patching, instantaneous endpoint analytics, and additional security features like vulnerability assessment, encryption, and web filtering, it helps strengthen an organization's overall security posture while ensuring compliance and streamlined endpoint management.
Free Trial: 30 Days.
Suricata
Suricata is a free intrusion detection tool. It is an open-source tool based on a network intrusion detection system (NIDS). Therefore, we use Suricata to detect identified threats and malicious activity in real-time. It uses a Signature-based method to identify the known threats or intrusion.
Blumira
Developers designed Blumira to detect threats and malicious activities across cloud services and on-premise devices. It can monitor the IT infrastructure continuously to detect any intrusion. Similarly, it is a SIEM platform that detects an in-progress attack and stops the attack.
Free Trial: 14 Days.
Cisco Stealthwatch
Cisco designed Stealthwatch with NIDS and HIDS. In addition, it is compatible with Windows, Linux, and MacOS operating systems. Cisco Stealthwatch is an intrusion detection system that does not require an agent enabling to grow business requirements. However, it uses machine learning to create baselines of patterns which is acceptable. One of the best features of this tool is that it can also detect intrusion and suspicious activities in the encrypted network without decrypting it.
Free Trial: 14 Days.
Conclusion
An Intrusion Detection System (IDS) is a very important tool to protect the network. There are many IDS tools available with different methods. For instance, IDS detects the intrusion and malicious activity in the network and alerts the administrator. However, with the help of the two Intrusion detection methods, it can detect known and unknown threats in the network. It monitors network traffic for a harmful activity or policy breaches. In conclusion, it does not prevent the attack but can alert any suspicious activities to a security specialist.
Also Read: List of 8 Network Segmentation Security Best Practices: You need to be aware about