The majority of the businesses today are online, which means there arises a need for a strong network to keep data safe.
You can’t stop any network intrusions coming in from hackers, but surely businesses can take measures to protect themselves from the same.
Snort and OSSEC are among the popular options which can help in detecting any intrusions.
Snort is an open-source network intrusion detection system with the ability to perform analysis on real-time traffic.
OSSEC, on the other hand, is a host-based intrusion detection system.
Because of its centralized cross-platform architecture, it has the ability to easily monitor and manage multiple systems.
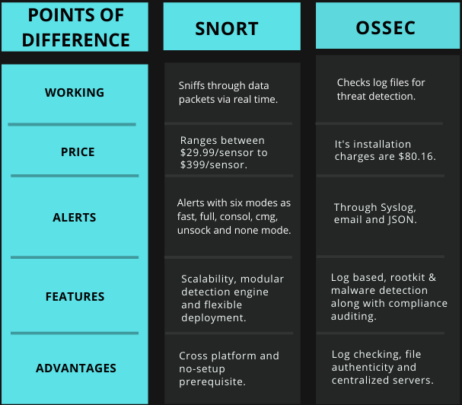
Snort vs. OSSEC: Detailed Difference Between the Two
Snort works by analyzing network traffic in real-time. It does so by sniffing through each passing data packet to detect any possibility of threats.
Because of this property, it can detect other threats like denial of services, buffer overflow and CGI(Common gateway interface).
After detecting suspicious activity, it immediately sends an alert to the Syslog, which is a separate file for alerts.
OSSEC, on the other hand, checks log files of systems for any threat detection.
It alerts the users on specific parameters, whenever it detects a threat to its operations.
Some of its alert parameters are given below:
- Detection of Trojan or rootkit.
- Upon failure of services.
- If packages are removed.
After every 6 hours, it checks on the binary files that have been provided with the unique hash MD5/SHA1 of the data. This process is called an integrity check, which protects the users from becoming bait to any threat.
Also Read: Kibana vs. Splunk: Know the Difference & Decide
Snort offers its two plans for the subscription.
- For personal subscriptions, it charges $29.99/sensor.
- For Business subscriptions, it charges $399/sensor
Whereas, OSSEC’s instalment costs around $80.16.
Snort provides its users with six types of alert modes. They are discussed as under:
- Fast: Reporting of timestamp, alert messages, and IP address source.
- Full: It includes an IP packet, IP header length, and sequence numbers.
- Consol: Fast alerts are printed here.
- CMG: Prints full alert on the console without saving reports to logs.
- Unsock: Allows us to forward the reports to different programs.
- None: No alert is generated.
Moreover, snort sensors use a snort configuration file, snort.conf, which defines snort variables, names of rule files and output plugins.
OSSEC provides alerts via
- Syslog: OSSEC manager is able to send alerts to one or more servers.
- E-mail: Email alerts are provided mainly under the single notification e-mail addresses, granular notifications, and daily e-mail reports.
- JSON: JavaScript Object Notation allows users to write alerts that allow other programs to use it.
Below mentioned are some of the key features of Snort:
- Scalability: Deployment on any network.
- Modular Detection Engine: Snort sensors have the efficiency of monitoring multiple machines from one location. This is the reason, Snort is being used as a security tool for tackling any unauthorized access.
- Flexibility in Deployment: Snort can be deployed in many ways.
Following are the key features of OSSEC:
- Log-based intrusion detections: Data is monitored from multiple logs.
- Rootkit and malware detection: Analyzes the overall process and file levels for detecting malicious applications.
- Compliance Auditing: Auditing with standards like PCI-DSS and CIS benchmarks.
- System Inventory: Keeps information about installed software, hardware utilization, and other information.
Following are the advantages of snort:
- A cross-platform, meaning it can be installed on various processors like Windows NT, Windows 2000 and HP-UX.
- Snort goes well with existing commercial products quite nicely not asking for any replacement in infrastructure.
Following are the advantages of OSSEC:
- Log checking.
- File authenticity and integrity checking.
- Centralized servers.
Snort finds its place ahead of OSSEC because of its feature of being cross-platform, meaning it can be easily installed on any processor.
This makes it easier for any of the organizations to even opt for this intrusion detection tool, even in the middle of their ongoing process.
Moreover, unlike OSSEC one has not to opt for new requirements for successfully running this intrusion system, as it goes well with any existing architects installed within an organization.